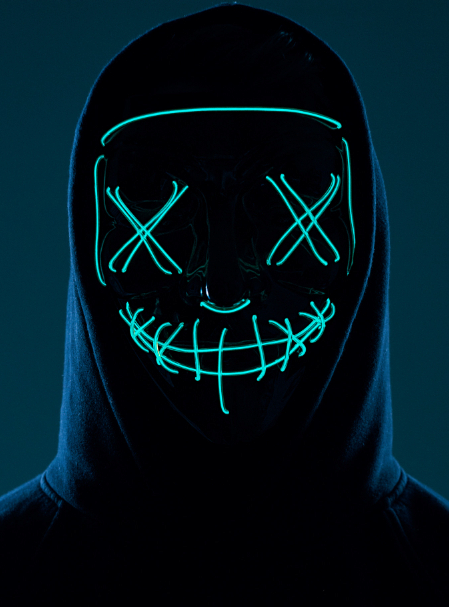
During a review of Shadow Network communications, investigators identified an image that may contain a concealed payload. The visible file does not immediately reveal any suspicious content, but image-based hiding techniques are commonly used to conceal flags, phrases, or operational notes.
Your task is to inspect the artifact and determine whether hidden data exists beneath the visible surface.
“Anyone can lock a message. Real hackers hide the door.”
— Cryptastic Crypto King
Hidden data may be embedded using steganography rather than traditional encryption. This means the message may not appear in the page source, visible text, or standard file preview. Investigators may need to inspect the file with stego tools or extract hidden content from the artifact directly.
Consider whether the image is simply decorative, or whether the pixels may be carrying information that the human eye cannot detect.